ThreatSwift CSIRT COMMANDO
Central Intelligence & Response built for CERT/CIRT, telecom, government, regulators, and SOC teams—so you can detect faster, investigate smarter, and coordinate action with control.
Get to Know About Our Flagship Product
CSIRT COMMANDO turns high-volume security signals into prioritized incidents and guided investigations—then produces reports and advisories that can be safely shared across tiers.

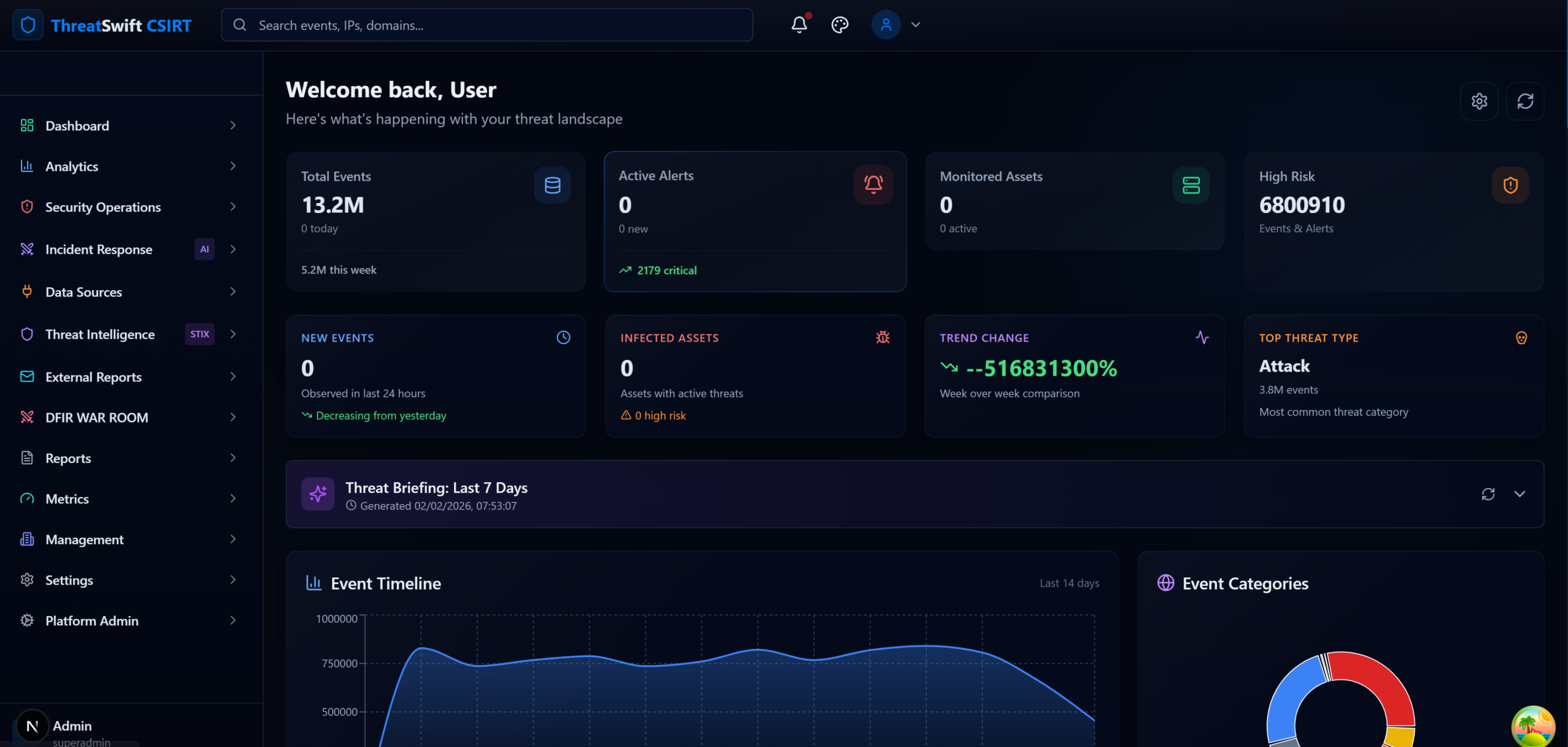
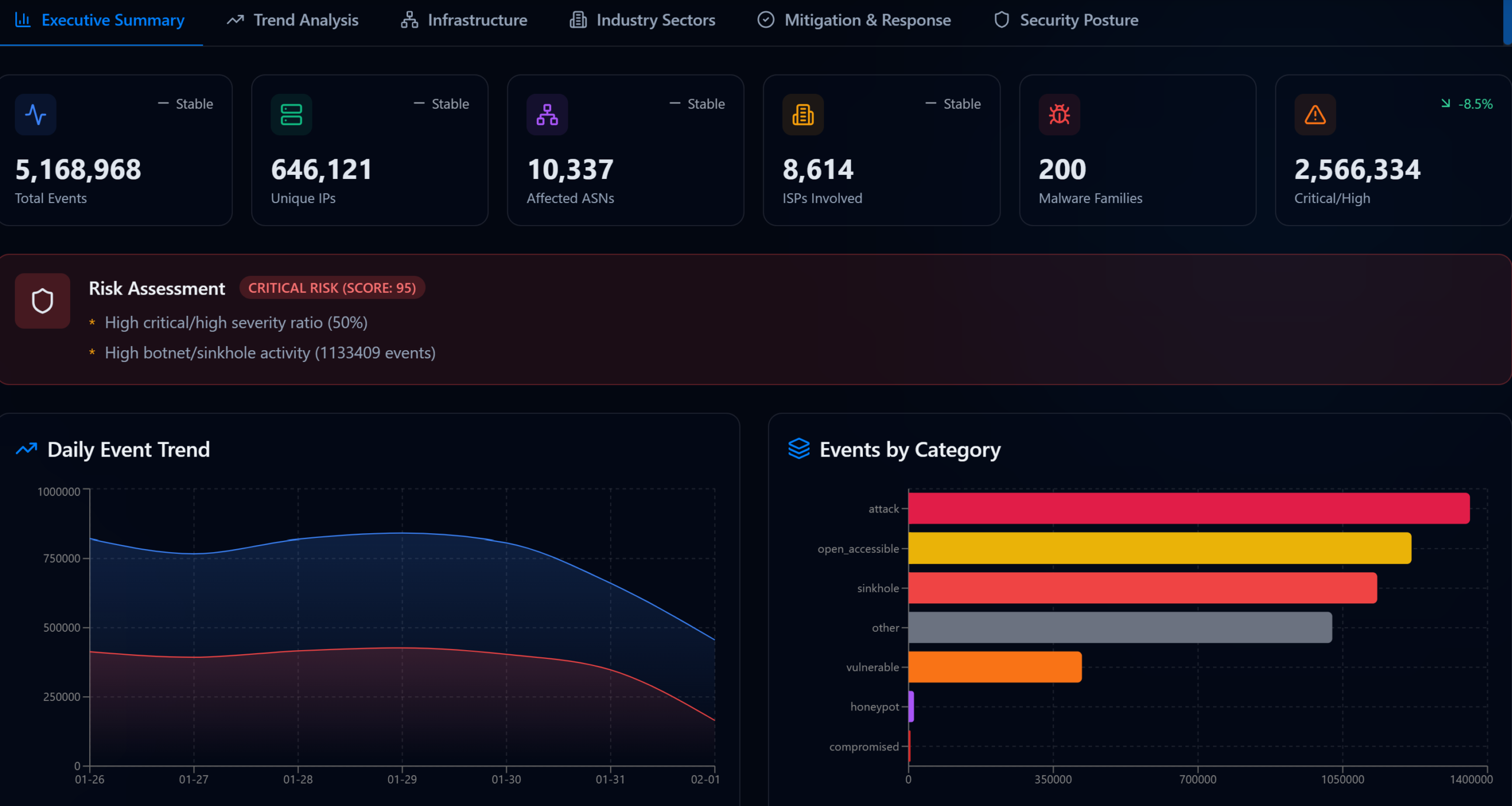
Nationwide Multi-Entity Visibility
Real-time view of security and compromised events.
Rapid search by IP, ASN, country, domain, malware, report type.
Risk-based prioritization to focus limited analyst time

Botnet & Malware Infection Analysis
Infection mapping and C2 relationship visibility.
Campaign clustering to support coordinated containment and advisories.

Early Warning That Drives Action
Continuous correlation across integrated sources.
Millisecond-level processing notification once signals received.
Escalation-ready workflow for high-risk threats.

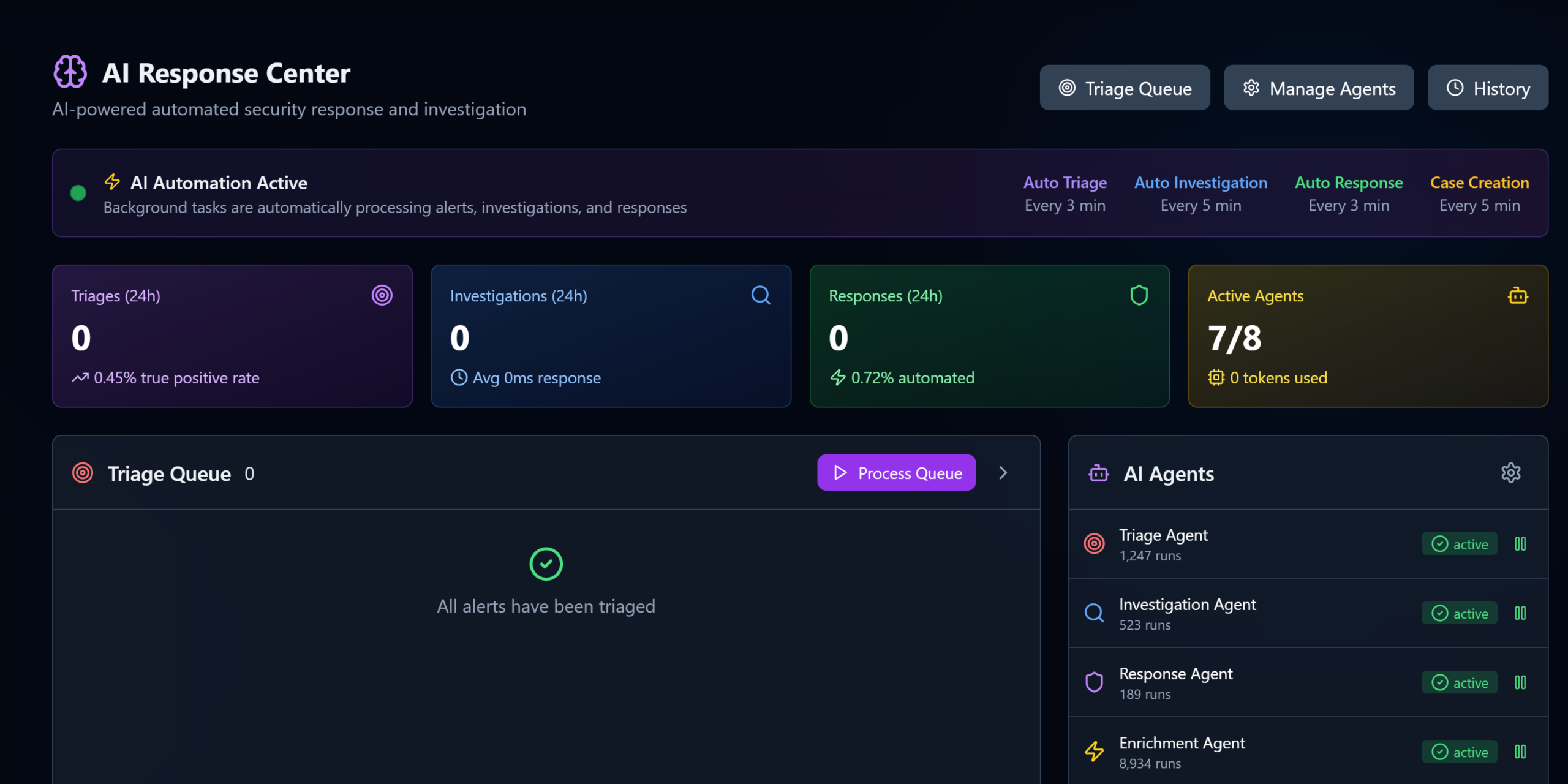
Incident Workflow Built for Real Operations
Structured pipeline: intake → triage → analysis → investigation → containment → reporting → closure.
Queue-based assignment and team visibility.

AI-Assisted Investigation & Remediation Guidance
Triage assistance and severity scoring.
Attribution cues and relationship mapping.
Guided playbooks and recommended next steps.

Reporting & Controlled Intelligence Sharing
Leadership dashboards and operational metrics.
Sector/entity reporting views.
Policy-controlled dissemination aligned to roles and authority.
Who are making the best out of CSIRT Commando
CERT/CIRT Teams
Command center visibility, multi-sector coordination, and governed dissemination.
Telecom SOCs
High-volume event handling and rapid infection/campaign visibility.
Regulators
Sector-wide reporting and measurable operational metrics—without compromising confidentiality.
MSSPs
Multi-tenant workflows, standardized investigations, and client-ready reporting.
SMEs
A guided approach to triage and investigation—without needing a large team.

What Our Customers Think About CSIRT Commando
Trusted by the incident response team members all over the world.
“We deal with high-volume events every day, and the biggest problem was separating real risk from noise. CSIRT COMMANDO made a noticeable difference by correlating indicators, surfacing infection patterns, and pushing actionable alerts fast. The botnet and C2 relationship views helped our team understand campaigns quickly and take focused action instead of chasing isolated alerts.”
Esther Howard
Head of Security Operations, Ireland
“CSIRT COMMANDO improved our speed and consistency across customers. The triage queue, investigation pipeline, and AI-assisted recommendations helped our analysts follow the same process every time; especially during high-pressure incidents. Reporting became cleaner and faster, and we were able to deliver more value to clients without expanding the team.”
Brooklyn Simmons
SOC Manager, MSSP